
Source: LaylaBird/E+ via Getty images.
A recent study conducted by 451 Research from S&P Global Energy Horizons examines cloud-specific information security pain points, the budget allocated to address them, how that budget is allocated between hyperscaler-specific security services and third-party tools, the cloud marketplace security offerings implemented, and the features influencing the implementation of software-as-a-service security offerings.
The Take
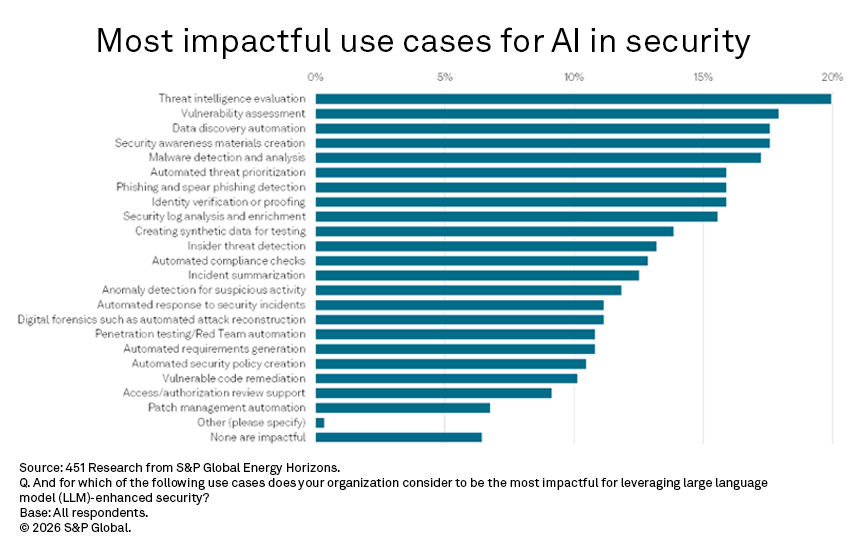
AI for security, or using large language model capabilities to improve security tooling, is permeating several organizations’ security product categories, a recurring theme since generative AI copilots emerged in 2023. When asked where teams are using LLM-enhanced security in their tooling and processes, the top responses are for malware detection and analysis (as in extended or endpoint detection and response), automated response to security incidents (such as a SecOps platform leveraging agents to automate common tasks), automated compliance checks and vulnerability assessment.
When the results are compared to a companion question asking where LLM-enhanced organizational security is having the greatest impact, the only commonality in the top four is vulnerability assessment, ranked second. Leveraging AI here may be prescient, as frontier AI models are showing aptitude for identifying security vulnerabilities. For example, Anthropic has initiated Project Glasswing in partnership with major security and technology providers, over concerns about the unreleased Claude Mythos model’s potential to identify exploitable weaknesses. Threat intelligence evaluation is number one, data discovery rounds out the top three, and creation of security awareness materials is fourth. Since OpenAI released ChatGPT in 2022, GenAI interfaces have been used for word smithing and graphics creation, key parts of creating educational materials. The commonality among the other three categories is more direct: They represent data analysis challenges, where AI holds promise in delivering context from massive data volumes.
The delta between implementation and impact raises a key question relevant to long-term security compliance issues like data discovery, which is characterized by a difficult and somewhat manual challenge: cataloging, permissioning access and protecting sensitive information. If impact lies in the messiness of data asset classification, why aren’t emerging AI capabilities more widely leveraged there? Is AI being applied to the most straightforward use cases, the most marketable ones, or the most intractable issues in organizational information security?
Summary of findings
Cloud security in general is the top cited pain point for information security managers, and a lack of security tooling to manage across multiple cloud providers is the most cited issue under that umbrella (21%). An organization of scale may have a primary cloud provider, but it almost certainly has a second or third provider too, based on business needs. That situation necessitates managing proprietary security stacks of cloud-provider-specific tools, which is a challenge given that cloud security skill sets are generally difficult to hire for in security teams. When one considers this as a top pain point, it becomes clear why Google, for example, has been so clear after recently closing its acquisition of Wiz that the offering remains a multicloud security tool despite now being owned by one of the major cloud providers. Managing cloud configurations, a key consideration addressed by the cloud security posture management (CSPM) and related cloud-native application protection platform (CNAPP) markets, is in second (19%), and compliance-related issues are in third.
With this multi-cloud security issue in mind, third-party security tooling generally enables this meta-level, or “above the clouds” level of security management. About two-fifths (39%) of respondents specifically note use of these tools and report that 44% of these are designed to work in a multi-cloud environment. About two-thirds (65%) of respondents report spending on premium security offerings from the cloud provider itself, which accounts for 37% of the security budget allocated specifically to cloud security. In the next 12 months, 36% of respondents plan to increase spending on third-party cloud security offerings, and 59% plan to increase spending on premium cloud services from cloud providers. Some of that spend will undoubtedly be made via a cloud marketplace. Currently, secure VPN and data recovery lead the security-style offerings available via marketplaces, with CSPM third at 31%, a key response to the difficulty of managing cloud configurations expressed in the cloud security pain points.
More than half of respondents (51%) note there are no restrictions on which applications can be placed in the cloud, meaning the implementation of security tooling to maintain the cloud posture must be determined. Many of those tools, such as CNAPP, are poised for continued growth to meet those requirements, with 28% of respondents currently piloting such solutions. Cloud hardware security modules continue to be one of the more implemented security controls, at 31% in-use. Just over a third (38%) of respondents’ organizations are still limiting cloud use in some way, noting that risk considerations do affect whether a workload can be hosted in the cloud. Fortunately, most respondents feel their security monitoring architecture in the cloud would be the first way they would learn that something is wrong (65%), versus those who somewhat unrealistically believe the cloud provider itself would alert them to a security issue (30%).
The features that drive spending on solutions to maintain an appropriate SaaS security posture are led by those that enable implementing multi-factor authentication (32%). This identity-management-based protection leads compliance reporting (21%) and the more table-stakes of application discovery and asset management (20%), rounding out the top three most cited features. User activity monitoring (20%) and data loss prevention (19%) are also prominent in security leaders’ minds when selecting these tools.
Want insights on Infosec trends delivered to your inbox? Join the 451 Alliance.

