What’s the biggest security pain point facing companies today?
According to the 451 Alliance, staffing is a big one.
In a recent survey of IT decision makers around the world, 66% of respondents reported there were not enough information security personnel at their organizations.
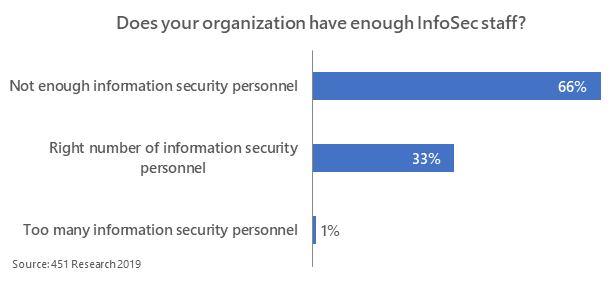
Not only are these organizations understaffed, but respondents also suggest that the existing information security staff are unable to adequately address the many challenges they face.
Influencers
Who are the most influential players when investing in information security?
62% of respondents suggest that IT leadership are the most influential people when deciding to invest in information security. Executive management (e.g., CEO, COO, Board) and Chief Information Security Officers (CISO)/Chief Security Officers (CSO) are also considerable influencers, at 61% and 32%, respectively.
Staff Additions
In the next 12 months, 25% of organizations plan to resolve this issue by making an addition to their information security staff. While this may seem like a simple resolution, recruiting is not always a quick fix.
In fact, recruiting information security personnel is rather difficult – demand exceeds supply.
When faced with an information security personnel shortage, 44% of organizations utilize contractors and consultants, while 22% utilize IT outsourcers.
Although outsourcing may seem like less of a headache, organizations must eventually reduce the proportion of outsourced IT in order to overcome the staffing shortage in the long term.
Worth the Investment
A reoccurring theme was presented across a few senior-level executives when asked their view on compensation, and their organization’s willingness to invest in information security personnel:
“[With security talent, there] is just simply a shortage. There’s a number of low-level security people, but when you get to the higher levels, it’s difficult. But… even with the scarcity, I think organizations don’t want to pay,” said one 451 Alliance member in a qualitative research interview.
Another tech executive shared a stumbling block when it comes to hiring InfoSec professionals, rooted in how we categorize their line of work.
“[Regarding] the appropriate compensation model and salary for information security: part of the problem is everybody throws security into a big bucket.
You wouldn’t do that with attorneys, because you have corporate attorneys, and you wouldn’t ask your corporate attorney about your divorce.
Well, there’s different categories of information security people and we’ve done a horrible job defining [those].”
Reorganization
While additions to staff may help enterprises get back on track, reorganizing the existing structure could also alleviate some issues with information security personnel workload.
Our members have commented:
“[The embedded security role] doesn’t work because [for example] the operational embedded team report to operational towers, and operations always takes priority over security.
So those people are either constantly bucking against their tower or they’re orphaned out, and they feel stranded, or they just give up and they water down security so it’s production-friendly and makes their boss happy.
And so it’s a lose-lose scenario.”
“[We] have tried to push this embedded security people [concept]… And that’s been pretty ineffective. It’s pretty hard to get someone to own a security role when they’re in a production team that security is their last concern.”
14% of the 451 Alliance members claim their organizations are either currently undergoing reorganization in the existing structure of their information security team, or are expecting to in the near future.
Want the inside scoop on infosec trends?
Join the 451 Alliance for exclusive research content. Do I qualify?