
Source: MohamadFaizal/Technology via Adobe Stock.
The concept of a platform that consolidates multiple functionalities is hardly new in cybersecurity. In a market characterized by fragmentation, it has long been a product strategy that embraces consolidation. While consolidation often serves a vendor’s growth priorities through the addition (organically or by acquisition) of new or emerging functionalities, a platform strategy would not be successful if it did not answer customer needs first and foremost.
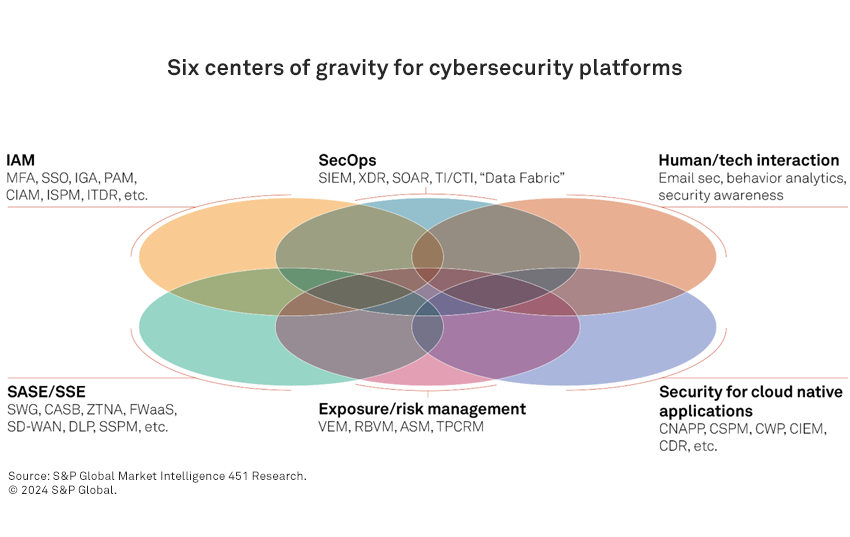
Much of the attention on cybersecurity platforms focuses on those serving the security operations center in threat detection and response, but there are other security domains that platforms have gathered around — highlighting the “centers of gravity” that characterize security platform evolution.
The take
The security market’s fragmentation partly reflects how it evolved. Emerging adversary techniques and technological innovation have driven awareness of new security needs. This can introduce opportunities for new startups and product segments. Capturing these new spaces is the objective of acquirers’ organic and inorganic growth — and thus a major motivation for venture-backed plays. Consolidation helps reduce the complexity of a plethora of tools, offering a “single throat to choke.” However, platforms must go beyond consolidation, to ultimately integrate information and action across functionalities, reflecting the sequence of processes customers follow when pursuing a comprehensive security strategy.
Six degrees of integration
In this blog post, we aim to summarize six of these centers of platform gravity in cybersecurity, as well as additional areas we are watching for their impact on shaping the market. Synergies are evident, but platforms have their limits. They must also navigate the “paradox of success” by mitigating the concentrated risk introduced when consolidation is widely adopted.
Across the cybersecurity landscape, certain focal points have crystallized platform trends. Others may yet follow, but today, six are having a notable impact on the evolution of the market (see figure). While not a strict depiction of synergies and overlaps, the diagram below suggests the many intersections.
1. Security operations, threat detection and response. One of cybersecurity’s most familiar platform venues, SecOps represents the responsive side of security, where organizations monitor for threats, detect and correlate evidence of being targeted, and handle response activities such as asset protection and incident investigation. Security information and event management (SIEM) has long been an anchor for this capability, centered largely on the collection of log data, and expanded with various approaches to anomaly and threat detection.
Recently, tools that gather telemetry directly from distributed sources such as endpoints and network systems have made threat detection and response more actionable at the point of contact with a threat. We have seen these platforms evolve to embrace multiple techniques in extended detection and response (XDR), disrupting legacy incumbents such as SIEM and giving rise to new security market leaders.
XDR platforms often incorporate log management and SIEM functionality to embrace not only this aspect of detection, but also correlation, threat hunting and historical analysis, as well as to support initiatives such as audit and compliance. SecOps platforms have been augmented further by workflow and automation tools to help security teams manage detection and response activities — with artificial intelligence playing a prominent role in the field’s evolution.
2. Cyber exposure risk management. If SecOps platforms are the reactive side of security that responds to threats, cyber exposure management is the more proactive side of assessing risk posture and remediating exposures. Its roots are in vulnerability management, long supported by the two pillars of assessment and remediation. Other functionalities that enable a more comprehensive awareness of exposure and asset inventory include attack surface management and third-party cyber risk management.
With potentially thousands of security vulnerabilities in any digital environment, the ability to prioritize remediation has become a focus. Although prioritization has long been an aspect of vulnerability management systems, newer risk-based vulnerability management vendors have emerged in response to this need, applying additional inputs such as active exploits in the wild, and other factors contributing to more effective prioritization. Increasingly, practical and evolved approaches to cyber risk measurement are shaping this space.
3. Security for cloud-native applications. With the proliferation of cloud-native assets, the need for protection and security telemetry specific to them has grown as well. A highly elastic cloud-native environment can scale at daunting speed. As cloud-native security data has burgeoned, so has the need to assess exposures, mitigate cloud-specific threats, and manage access entitlements. This has led to providers building portfolios in cloud security posture management (CSPM), cloud identity and entitlements management (CIEM), and cloud detection and response (CDR). While labels like CNAPP (cloud-native application protection platform) point to the overall platform theme, others distinguish between the proactive aspects of CSPM and the more reactive and operational aspects of a CNAPP portfolio.
4. Secure access service edge/security service edge. During the pandemic, demand for secure remote access increased substantially, considerably adding to the vendor opportunity for integrating private network access with the security functionality previously found primarily in corporate networks, extending the enterprise security investment to any accessible venue.
Capabilities may include more sophisticated approaches to network access control, such as zero-trust network access, software-defined wide-area networking, data loss prevention and secure web gateway. Those with an emphasis on security for SaaS assets may offer functionality such as cloud access security broker capability or SaaS security posture management. Because this platform model lends itself to expansion based on changing secure corporate access needs, additional functionalities may be further incorporated.
5. Identity and access management. If the above centers of platform gravity are more operationally focused, they often have one thing in common: Access control is on the front line of both the proactive and responsive aspects of cybersecurity — as a key control, and often as a primary target of attack. This raises the significance of IAM as a center in its own right.
IAM systems have long had platform characteristics. It is not just a central resource integrated with multiple assets, but critical for operational availability throughout an environment. As demands on access control have evolved, vendors offering workforce IAM (WIAM) technology have expanded their range, incorporating techniques such as multifactor authentication, privileged access management, and identity governance and administration. An emphasis on zero trust in implementing control aims to reduce exploitable gaps in traditional approaches. WIAM may interface with identity threat detection and response (ITDR) and identity security posture management (ISPM) for hardening user accounts against exploit, and detecting attempted or successful account takeover.
Distinctions between WIAM and IAM for business customers of digital services (customer IAM) may extend accounts into the millions, and prioritize reducing friction, completing transactions and integrating payments. Yet there is an actionable middle ground between workforce personnel and purely external entities. Extending access to third parties such as contractors, partners and suppliers must be handled differently — and business-to-business IAM is an emerging aspect of IAM platform extensions.
6. Human-technology interaction. This is a more recent center for cybersecurity platforms, rooted in securing enterprises against one of the most active threat vectors: malicious email, phishing, spam and other risky content targeting an organization’s people. While email security and anti-phishing may be at the heart of this trend, protecting against malicious content is only half the battle. How people interact with it is another — and in some respects, is far more challenging.
Well-crafted attacks may appear to be completely legitimate and entirely benign. Security awareness training and other emerging techniques can make threat recognition more actionable, but enterprises must also recognize when human activity could introduce a threat. This creates opportunity to extend behavioral analytics to such a platform strategy, and it has factored into recent acquisitions. Visibility into the information that people and organizations reveal about themselves may play a role in recognizing and mitigating risk, introducing the potential for digital risk protection.
The paradox of success
Given that security platforms have been evolving for decades, there will be further centers of gravity that may emerge. Vendors of data security technology, for example, are among the largest in the market. Unlike other security platforms, pure-play data security vendors often have diffuse boundaries with built-in security controls factored into applications such as SaaS platforms. Yet here, too, we see trends like data security posture management, with a growing number advocating their approach as a “data security platform.”
Vendors of application security technologies may offer a portfolio of tools, from software supply chain assurance to static and dynamic application security testing. While these tools may integrate functionalities, their use often occurs sequentially when invoked in development and deployment processes — and may play roles in the organizationally specific toolchains for DevSecOps.
There is also the question of the structure that platforms can take. In a “vertical” model, the platform would incorporate patterns seen in other centers of gravity, but specifically applied to the platform’s focal segment. An example would be identity, which has recently capitalized on the themes of posture management (and thus ISPM), threat detection and response (and thus ITDR), and attack surface management (and the resultant identity attack surface management).
Similarly, for CSPM and CDR, in a more “horizontal” model, a cyber exposure and risk management platform might assess exposure and risk across the digital landscape. However, in implementing controls to mitigate risk, capabilities in adjacent centers of platform gravity may be added, such as cloud-native applications or identity (both evident in CIEM). The overlap between email security and the behavioral analytics applied in threat detection and response is also evident in the rise of this functionality in the human-technology interaction plays from email security and anti-phishing providers.
The case of cyber exposure and risk management already illustrates some of the limits of platform reach. While these tools can highlight and prioritize the need for exposure remediation, deploying mitigation like patching is often more the responsibility of IT operations teams — although platform providers have added patching functionality to offer expanded options in seeing risk remediation through to completion.
Other factors, such as customer concerns about the potential for vendor lock in, can limit the appeal of a platform play. Ironically, one risk is the paradox of success. The CrowdStrike outage made clear that a widely adopted platform may concentrate risk when a failure affects critical dependencies. This is far from affecting cybersecurity alone, however. The short-term fallout from this particular incident is already evident, but it remains to be seen whether future events will galvanize action to mitigate such risks, or impact the long-term platform evolution that has been such a force up to now.
Want insights on Infosec trends delivered to your inbox? Join the 451 Alliance.
Want insights on consumer technology trends delivered to your inbox? Join the 451 Alliance.
This content may be AI-assisted and is composed, reviewed, edited and approved by S&P Global in accordance with our Terms of Service.

